
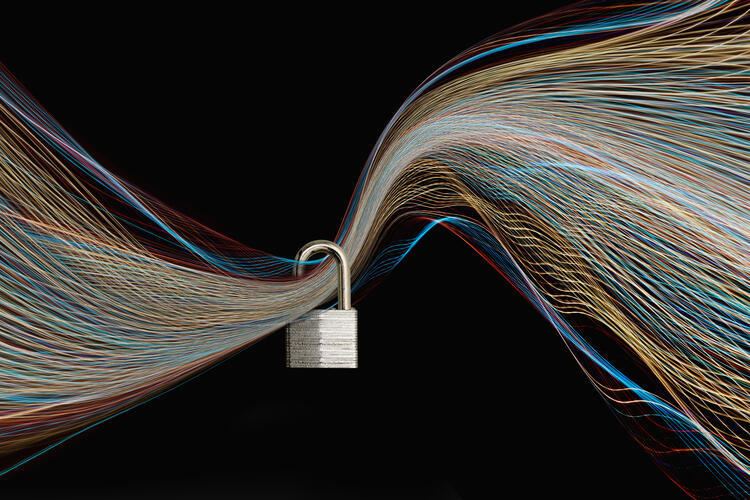
Cyber Assessments
Verify Your Defenses and Security Measures With a Professional Cybersecurity Assessment.
View Your Business's Financial, Website, and Security Risks
It's hard to feel relaxed about your cyber protection unless you continually check to ensure that your defenses are sound. EisnerAmper has developed strategies to help you feel secure about your cybersecurity risks.
A cyber assessment gives you a bird's eye look into your network. It uncovers vulnerabilities that you might not know about.
Whether it's peeling back the layers of your IT systems, scanning websites and the dark web for stolen information, or a policy review, we have the same goal. We strive to highlight risks to your organization and establish a secure infrastructure.
Every gap in your security could be putting millions at risk, including you, your employees, and your customers. Contact us today to learn more about getting a cybersecurity risk assessment and our managed IT services.
We Start with a Comprehensive IT Assessment
EisnerAmper implements a Financial Risk of Security Technologies (FiR$T) Look. Our proprietary tool was created by our seasoned IT and risk management specialists. The results provide you with a checklist of your current IT gaps.
We also report financial impacts based on your current position. You can find your results in one easy-to-use dashboard.
FiR$T Look Focuses On Three Categories of Risk:
| FOUNDATIONAL | OPERATIONAL | PROACTIVE |
|---|---|---|
|
The Foundational Look considers the core security measures that are the building blocks to an overall risk management plan. These are areas that are essential to having the basics
|
The Operational Look score takes into account security measures that dynamic growing companies should focus on to increase their security posture. As a business is running these are the next group of areas to be thinking of:
|
The Proactive Look considers more advanced security considerations geared at forward thinking organizations that are actively preparing for future security threats. Forward thinking, a business should embrace these areas:
|
Once we've received your results, our cybersecurity guides will create a roadmap. We'll recommend how your business can best allocate its IT budget to achieve the largest ROI.
Web Look – A Website-Focused Assessment
Our Web Look assessment is designed to protect your most important digital assets. Hackers can take advantage when companies move data to the cloud, generate business online, or provide web-based solutions. Businesses need to have a plan to secure their digital products.
Our Web Look assessment utilizes proprietary technology. We discover vulnerabilities before hackers can. We'll provide a remedy plan for any risks that we uncover.
Cyber Look — A Comprehensive Assessment Package
Our Cyber Look gives businesses a complete view of their cybersecurity posture. It gives business owners insight into how cybersecurity issues could impact their company. Cyber Look is ideal for businesses of any size, in any industry.
1. First Look Assessment
Without having to be at your location, our team provides observations and recommendations to address deficiencies and gaps from our years of successful engagements. In one painless process, this assessment uncovers your company’s IT risk and subsequent financial implications.
2. Web Application and Vulnerability Scan
We conduct a dynamic software cybersecurity scan and assessment to identify security gaps and misconfigurations with externally facing web applications and infrastructure and provide advice on those gaps.
3. Corporate Email/Credentials Scanning on the Dark Web
Intentionally hidden, the dark web is a hot bed for stolen personal information hackers use to exploit their targets for ransom. In this scan, we look for your employees’ and clients’ confidential data, like password information. If found, we provide recommendations for future prevention.
4. Policies and Procedures Review
Your ability to secure private information and maintain a strong infrastructure is only as good as the policies and procedures in place. Here, we examine all current documentation and policies and/or those in the process of being implementing and provide recommendations for attaining proper information security program standards.
How Our Process Works
Step One:
Start a Conversation
Send us an email or fill out our online form to get more information.


Step Two:
Pick Your Option
We'll help you select the best assessment plan based on your needs and budget.
Step Three:
Feel Secure
You can move forward knowing that your company is taking significant steps to mitigate cybersecurity risks.
Since working with the team, we now have peace of mind that we have the appropriate security systems in place and someone there for us when we need it. They empowered us to do our job and worked with us to implement the proper controls for our specific business needs.
We're the Leading Outsourced IT Company
EisnerAmper provides innovative solutions to businesses of every size in multiple industries. Our goal is to protect your company from hackers while securing your data.
What's on Your Mind?
Start a conversation with Rahul
